Federal agencies and contractors aren’t just encouraged to train their workforce on cybersecurity, they’re required to. The foundation for that requirement comes from NIST security awareness training guidelines, primarily outlined in publications like SP 800-50 and SP 800-53. These documents spell out what an effective program looks like: who’s responsible, what topics to cover, how often to train, and how to measure whether any of it is actually working.
But understanding what NIST expects is only half the challenge. The other half is building a program that meets those standards without burying your team in manual processes. That’s where a purpose-built LMS like Axis LMS from Atrixware fits in, giving organizations the tools to deliver, track, and document compliance training against frameworks like NIST, with automated reporting and certification tracking built right in.
This article breaks down the core NIST publications that govern security awareness training, the roles and responsibilities they define, and the concrete steps you need to take to build a compliant program from the ground up. Whether you’re starting fresh or tightening up an existing initiative, you’ll walk away with a clear, actionable roadmap tied directly to what NIST actually requires.
What NIST means by awareness, training, and education
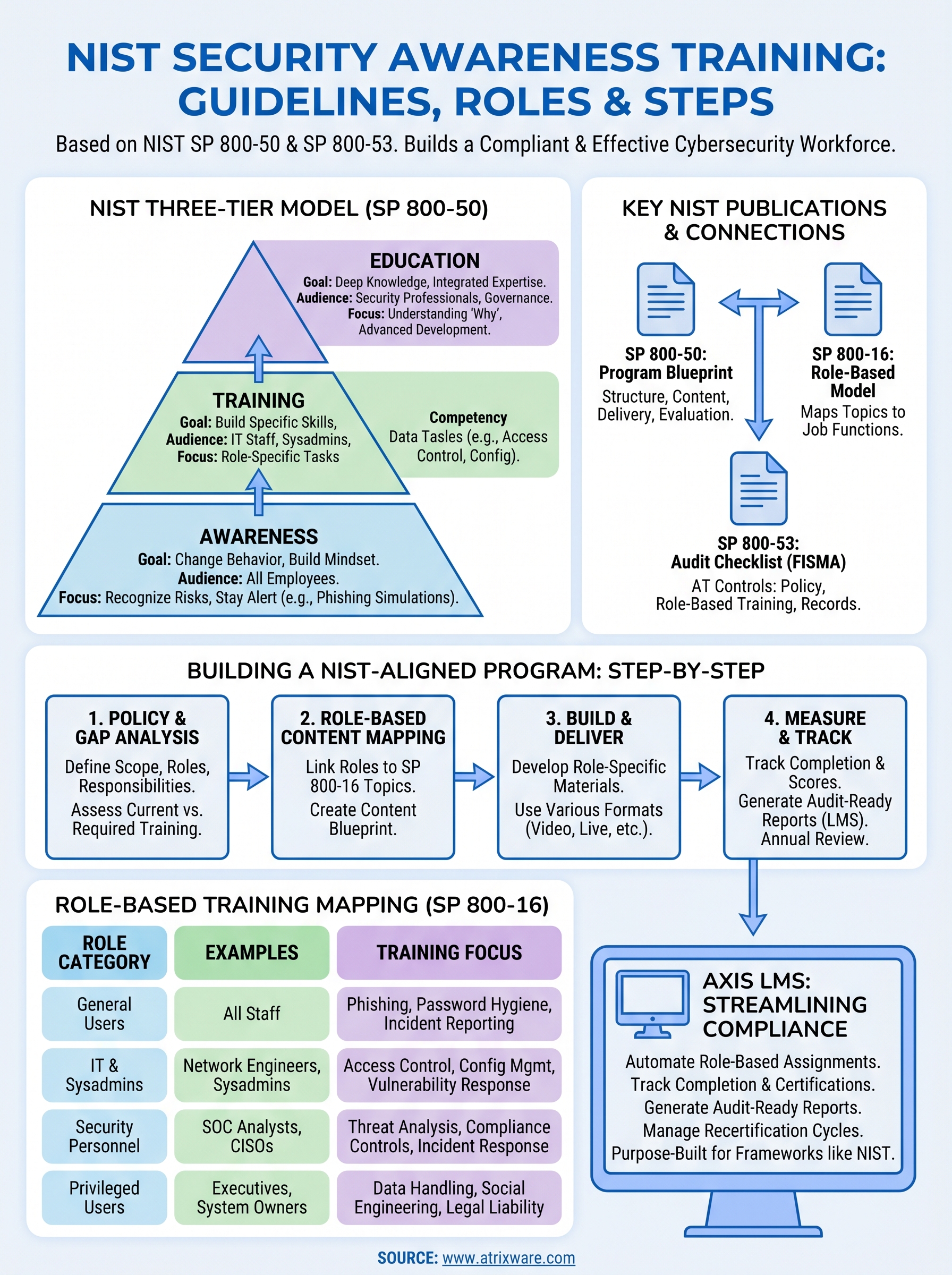
NIST draws a clear line between three related but distinct concepts: awareness, training, and education. SP 800-50 defines these as separate tiers in a continuum, not interchangeable terms. Understanding the difference matters because it directly shapes how you design your program and who receives what type of content.
The three-tier model NIST uses
At the base level, awareness is about changing behavior through exposure. NIST describes it as an effort to get people to recognize security as relevant to their daily work. You’re not teaching skills here; you’re building a mindset. Think of reminders, brief videos, and phishing simulations that keep security top of mind for the average employee who doesn’t work in IT.
Training steps up from there by actually building skills. SP 800-50 describes training as teaching people to perform specific security tasks, not just recognize threats. This is where your IT staff, system administrators, and anyone handling sensitive data need hands-on, role-specific instruction that goes beyond general awareness content. The goal is competency, not just familiarity.
NIST separates awareness from training because knowing a threat exists and knowing how to respond to it are fundamentally different outcomes.
How education fits into the picture
Education sits at the top of the NIST model and is reserved for individuals pursuing deeper security knowledge, typically your security professionals and those in governance roles. SP 800-50 frames it as understanding the "why" behind security practices, integrating concepts from multiple disciplines into a coherent body of knowledge. You won’t deliver this through a standard course; it’s tied to degree programs, certifications, and advanced professional development.
Knowing where each group falls in this model helps you allocate resources accurately across your workforce. Here’s how the three tiers typically map to different employee categories:
| Tier | Audience | Primary Goal |
|---|---|---|
| Awareness | All employees | Recognize risks and stay alert |
| Training | IT staff, system admins, data handlers | Build specific, job-relevant security skills |
| Education | Security professionals, governance roles | Develop deep, integrated security expertise |
Your NIST security awareness training program needs to account for all three tiers, even if most of your workforce only requires awareness-level content. Treating every employee as the same type of learner is one of the most common mistakes organizations make when building their NIST-aligned programs, and it’s one that auditors and reviewers will notice quickly.
Why NIST-aligned security awareness training matters
Non-compliance with NIST standards isn’t just a documentation problem. If your organization handles federal data or works with government contractors, failing to meet the standard carries real consequences, from contract termination to legal liability. A well-built NIST security awareness training program protects your organization on two fronts: it reduces actual security risk and demonstrates due diligence to auditors.
The compliance stakes are real
Federal agencies operate under the Federal Information Security Modernization Act (FISMA), which mandates security awareness training for all users with access to federal information systems. NIST publications like SP 800-50 and SP 800-53 define what that training must look like. If you’re a contractor or vendor serving a federal agency, those same requirements typically flow down to your organization through your contract terms.
Underdocumenting your training program doesn’t just create a compliance gap; it creates an audit risk that can cost you the contract.
Common scenarios where NIST alignment becomes mandatory include:
- Federal agency employees and contractors under FISMA
- Healthcare organizations referencing NIST under HIPAA security guidance
- Defense contractors governed by CMMC, which draws heavily from NIST SP 800-171
The security impact goes beyond checking boxes
Security incidents most often start with human error: a clicked phishing link, a misconfigured system, or a password shared carelessly. Structured training built on the NIST model gives your workforce the specific skills and habits needed to reduce those failure points.
Organizations that train consistently and role-appropriately see measurable reductions in successful phishing attempts and insider incidents. Your training program isn’t just a compliance exercise; it’s one of the most cost-effective risk controls your organization can implement.
The key NIST documents to know and how they connect
NIST has produced several publications that shape security awareness training requirements, and knowing which ones apply to your situation saves significant time. These documents don’t operate in isolation; they reference and reinforce each other, so understanding how they connect helps you build a program that satisfies multiple requirements at once.
SP 800-50 and SP 800-16: The training blueprints
SP 800-50, titled "Building an Information Technology Security Awareness and Training Program," is the primary document for designing and managing your program. It covers program structure, content development, delivery methods, and program evaluation, making it the go-to reference for anyone building a NIST-aligned initiative from scratch. SP 800-50 is where the three-tier awareness-training-education model originates.
SP 800-16 complements it by providing a role-based model for cybersecurity training. Where SP 800-50 lays out the program architecture, SP 800-16 maps specific training topics to specific job functions, giving you a practical framework for tailoring content to different employee groups. Together, these two publications give you both the structure and the content blueprint for your nist security awareness training program.
Reading SP 800-50 and SP 800-16 together gives you a far more complete picture than either document provides on its own.
SP 800-53 and the AT control family
SP 800-53 operates at the organizational controls level and is mandatory reading for anyone pursuing FISMA compliance. Within it, the AT (Awareness and Training) control family defines specific requirements your program must meet, including policy documentation, role-based training, and records of training completion.
Controls like AT-2 (Literacy Training and Awareness) and AT-3 (Role-Based Training) translate directly into program features: who gets trained, on what topics, and how often. SP 800-53 is what auditors check against, so treat it as your compliance checklist.
Roles, audiences, and training requirements to cover
NIST doesn’t treat your entire workforce as a single training audience, and neither should you. SP 800-16 maps security training requirements to specific job functions, which means your program needs to segment learners by role before you decide what content to deliver to whom.
Mapping roles to training requirements
SP 800-16 organizes users into two primary categories: general users and functional specialists. General users are everyone who touches an information system as part of their daily work, including administrative staff, finance teams, and managers. Functional specialists include IT staff, security personnel, and system administrators who carry direct responsibility for protecting systems and data. Your nist security awareness training program must handle both categories with meaningfully different content requirements.

Applying the same training content to a general employee and a system administrator doesn’t satisfy NIST requirements, and it won’t reduce your actual risk.
Here’s a practical breakdown of how roles map to training focus:
| Role Category | Examples | Training Focus |
|---|---|---|
| General users | All staff | Phishing, password hygiene, incident reporting |
| IT and system admins | Network engineers, sysadmins | Access control, configuration management, vulnerability response |
| Security personnel | SOC analysts, CISOs | Threat analysis, compliance controls, incident response |
| Privileged users | Executives with elevated access | Data handling, social engineering, legal liability |
What each group actually needs to cover
NIST expects your program to address threats and responsibilities relevant to each role, not deliver a generic course everyone clicks through in 20 minutes. General users need to recognize phishing attempts, handle sensitive data correctly, and know when to escalate an incident. IT staff need technically grounded instruction on access management and configuration security.
Privileged users often get overlooked, but they carry significant risk because their credentials provide elevated access. Your program should include targeted content for executives and system owners that covers the legal and operational consequences of a breach, not just the technical mechanics.
How to build a NIST-aligned program step by step
Building a NIST security awareness training program doesn’t require starting from scratch with a blank page. What it does require is a structured sequence that moves from policy through delivery to measurement, with each step grounded in what SP 800-50 and SP 800-53 actually call for.
Start with a needs assessment and policy foundation
Before you build anything, document the scope of your program in a formal policy. SP 800-53’s AT-1 control specifically requires a written awareness and training policy that defines roles, responsibilities, and update schedules. Once your policy exists, conduct a gap analysis to identify which user groups currently receive training, what topics they cover, and where your coverage falls short against NIST requirements.
Skipping the policy step is the single fastest way to fail a FISMA audit, even if your training content is otherwise solid.
Use your gap analysis to create a role-based content map that ties each audience segment to the specific topics SP 800-16 assigns to their job function. This map becomes your program blueprint and keeps content decisions anchored to documented requirements rather than guesswork.
Build, deliver, and measure
With your content map in place, develop or source training materials for each role tier. General user content should cover phishing recognition, password hygiene, and incident reporting. Role-specific modules need to address the technical and compliance responsibilities each group carries. Deliver content through a format your learners can realistically complete, whether that’s video-based modules, live virtual sessions, or scenario-based exercises.
Track completion rates and assessment scores against each learner’s role and document the results. SP 800-53’s AT-4 control requires you to maintain training records, so your LMS needs to generate reports you can produce on demand for auditors. Set a recurring annual review cycle to update content as threats and NIST guidance evolve.
A simple way to get started
Building a compliant nist security awareness training program is straightforward once you have the right structure and tools in place. The hardest part isn’t understanding what NIST requires. It’s managing the delivery, tracking, and documentation across dozens or hundreds of learners without losing control of your records.
Axis LMS handles all of that for you. You can assign role-based training modules, track completion and assessment scores, generate audit-ready reports, and automate recertification cycles from a single platform. Whether you’re building your program from scratch or replacing a process that depends on spreadsheets and manual follow-ups, Axis LMS gives your team the infrastructure that real NIST compliance demands. Take the LMS readiness quiz to find out exactly where your organization stands and what your next step should be.
