Most organizations use the terms data privacy vs data security interchangeably, and that confusion creates real risk. Privacy and security address fundamentally different questions about your data: who should have access to it, and how do you prevent unauthorized access? Getting either one wrong can mean regulatory fines, broken trust, or both. Understanding the distinction matters especially when your business handles sensitive information like employee records, compliance certifications, or learner progress data.
At Atrixware, we build Axis LMS to help businesses deliver and manage training programs, which means our platform handles personal and professional data every day. From tracking who completed a compliance course to storing assessment results, the line between keeping data private and keeping it secure is one we think about constantly. It’s a challenge we know our customers face too, whether they’re onboarding new employees, training channel partners, or selling courses externally.
This article breaks down what data privacy and data security actually mean as separate concepts, where they overlap, and where they diverge. You’ll find concrete examples that illustrate each one in practice, along with a clear framework for thinking about how both apply to your organization. By the end, you’ll have the clarity you need to evaluate your own policies and make informed decisions about protecting the data your business depends on.
Data privacy and data security defined
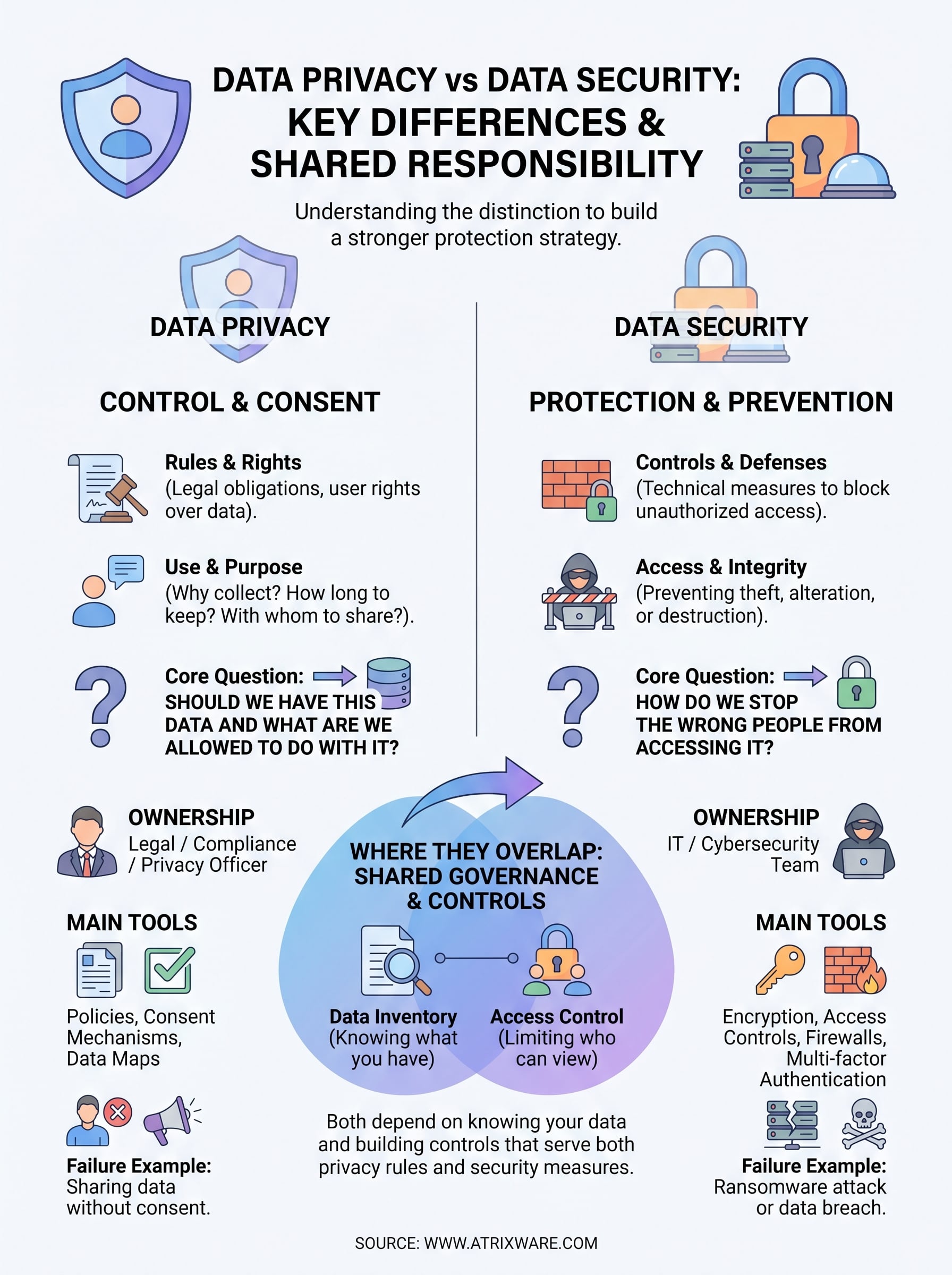
Before you can meaningfully compare the two, you need a clear understanding of each concept on its own terms. Data privacy focuses on the rights and expectations around personal information: who is allowed to collect it, how it can be used, and whether the people it belongs to have any say over it. Data security focuses on the technical and procedural measures that protect data from unauthorized access, theft, or damage. Treating the two as synonyms is where most organizations run into trouble, because understanding data privacy vs data security as separate disciplines is what lets you build a strategy that actually covers both.
What data privacy means
Data privacy is about control and consent. When someone provides their name, email address, or training completion records to your organization, they have a reasonable expectation that you will handle that information according to their wishes and applicable regulations. Privacy sets the rules: what data you can collect, why you can collect it, how long you can retain it, who you can share it with, and what rights the individual keeps over their own information.
Consider a learner who enrolls in a compliance course through your LMS. That person is handing over personal data. Your responsibility is to be transparent about how you use it, limit collection to what you actually need, and give that learner meaningful control over their record. Privacy regulations like GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act) translate these expectations into legal requirements with real financial penalties for organizations that ignore them.
Data privacy is fundamentally a people-first concept: it protects an individual’s right to know what is collected about them and to have a say in how it is used.
What data security means
Data security is about protection and prevention. Where privacy asks "should we have this data and what are we allowed to do with it," security asks "how do we stop the wrong people from accessing it." Security covers the tools, processes, and policies that prevent unauthorized individuals from reading, altering, or destroying your data, whether that threat comes from outside attackers, careless employees, or system failures.
Common security controls include encryption, access controls, multi-factor authentication, firewalls, and intrusion detection systems. In an LMS context, security means a learner’s assessment results can only be viewed by that learner and the administrators who need them, and that the system blocks anyone attempting to access records without valid credentials. These controls do not care about the legal or ethical rules around data use; they care about whether the data is technically protected from unauthorized access.
Security also extends to data integrity, meaning the protection of data from being altered or deleted without authorization. A course completion record that gets corrupted, overwritten, or silently modified is a security failure, even if no outside party ever read the data. Your security program is responsible for ensuring the data your organization holds remains accurate, consistent, and available only to those with a verified, legitimate reason to access it.
Key differences at a glance
The clearest way to understand data privacy vs data security is to recognize that they answer fundamentally different questions. Privacy is about rights and rules: what data you collect, why you collect it, and what rights individuals retain over their own information. Security is about controls and defenses: the technical and procedural measures that prevent unauthorized access, theft, or corruption of that data. Both matter to your organization, but conflating them leads to gaps in your strategy and exposure you may not even realize you have.

You can have excellent security controls and still violate privacy, and you can have a strong privacy policy and still suffer a breach. The two disciplines protect data in completely different ways.
The core question each one answers
Privacy asks "are we handling this data in the way the person it belongs to expects, and in the way the law requires?" Security asks "can we prevent unauthorized parties from accessing this data?" A company can answer yes to both, or yes to one and no to the other. An organization that encrypts everything but sells personal data to third parties without consent has strong security and weak privacy. An organization that publishes a thorough privacy policy but stores records in a plaintext database has good privacy intent and poor security execution.
These two questions also produce different kinds of failures with different remedies. A privacy failure typically looks like unauthorized data sharing, missing consent, or retaining records longer than policy allows. A security failure looks like a breach, a ransomware attack, or an insider exfiltrating records. Privacy failures usually require policy revision, regulatory disclosure, and legal response. Security failures require technical remediation, system patching, and incident response procedures.
Who owns each discipline in your organization
Privacy ownership typically sits with legal, compliance, or a designated privacy officer, because privacy is primarily a governance and policy function. Security ownership sits with your IT or cybersecurity team, because security is primarily a technical function. This natural split means the two can operate in silos unless leadership actively bridges them.
The table below captures the sharpest distinctions between the two:
| Data Privacy | Data Security | |
|---|---|---|
| Core question | Who can collect and use this data? | How do we block unauthorized access? |
| Primary owner | Legal / Compliance / Privacy Officer | IT / Cybersecurity team |
| Main tools | Policies, consent mechanisms, data maps | Encryption, access controls, firewalls |
| Key frameworks | GDPR, CCPA | ISO 27001, NIST Cybersecurity Framework |
| Failure example | Sharing data without consent | Ransomware attack or data breach |
Where they overlap in real organizations
Privacy and security are distinct disciplines, but they operate on the same data, which means they create shared obligations for your organization whether you plan for it or not. A single piece of personal information, like a learner’s name tied to a course completion record, is simultaneously a target for security threats and a subject of privacy rights. When you think about data privacy vs data security in practice, you quickly discover that the two disciplines rely on each other to function. Strong security without privacy governance means you are protecting data you may not have had the right to collect. Strong privacy without security means your policies exist on paper while the actual data sits exposed.

Where privacy and security genuinely depend on each other is in the controls you build to protect personal data, because those controls serve both goals at the same time.
When a breach becomes both a security and privacy problem
A data breach is the most visible example of how these two disciplines collide. What starts as a security failure, such as an attacker gaining unauthorized access to your training records system, immediately becomes a privacy failure the moment personal data leaves your control without the consent of the people it belongs to. Your IT team responds to the technical compromise, while your legal and compliance team must assess whether the breach triggers regulatory notification requirements under frameworks like GDPR or applicable US state laws. Both responses happen in parallel, and neither is optional.
This overlap also shows up in how your organization documents its controls. Regulators reviewing your privacy compliance will often ask about your security measures, because demonstrating you protect personal data means showing both that you follow the right policies and that you have technical safeguards in place. A privacy audit and a security audit draw from many of the same source documents: your data inventory, your access control policies, and your incident response plan.
Shared data governance requirements
Both disciplines depend on knowing what data you have and where it lives. You cannot protect data you have not mapped, and you cannot apply the correct privacy rules to data you have not classified. This means your data governance program, specifically your data inventory and classification process, directly serves both your privacy and security teams.
Access control is another area where the two overlap almost completely. Limiting who can view a learner’s personal record is a privacy requirement, but the mechanism you use to enforce that limit is a security control. Role-based permissions, authentication requirements, and audit logs all serve privacy goals while functioning as security tools.
Real-world examples you can relate to
Abstract definitions only take you so far. Seeing data privacy vs data security play out in familiar situations makes the distinction much easier to apply to your own organization. The examples below each show what a privacy failure looks like, what a security failure looks like, and why the two are not the same problem even when they occur in the same system.
A healthcare provider and patient records
Consider a hospital that stores patient records in a secure, encrypted database. Security controls are strong: the system requires multi-factor authentication, logs every access event, and encrypts data both at rest and in transit. Now suppose a hospital administrator shares a patient’s diagnosis with a pharmaceutical company without the patient’s knowledge or consent. No attacker was involved, no system was compromised, and no breach occurred in the technical sense. The data stayed secure. But the hospital violated the patient’s privacy, because information was shared without consent and outside the purpose for which it was collected.
A perfectly secured system can still produce a privacy violation the moment someone uses data in a way the person it belongs to never agreed to.
An employee training platform
Your organization runs an LMS to deliver compliance training to new hires. An IT administrator accidentally configures a permission error that allows any logged-in user to view the training records of every other employee, including certifications tied to disciplinary processes. No external attacker accessed the system. The data was not encrypted incorrectly. But the access control failure exposed personal records to people who had no legitimate reason to see them. That is a security failure, not a policy-level privacy failure, though it creates real privacy harm for the employees whose records were exposed.
An e-commerce account and a third-party data sale
You create an account on a retail website to complete a purchase. The retailer collects your name, address, and purchase history with your agreement, as disclosed in their terms at sign-up. Later, the retailer sells that purchase history to a data broker without notifying you or offering an opt-out. The database was never breached. No hacker touched your information. The retailer simply chose to use your data in a way that exceeds what you reasonably consented to. That is a privacy failure with potential regulatory consequences under laws like the CCPA, and it has nothing to do with how well the retailer’s servers were protected.
Laws, standards, and who owns what
When you compare data privacy vs data security, the regulatory and standards landscape is one of the clearest places to see how differently these two disciplines are governed. Privacy is largely shaped by law, meaning government bodies set the rules and impose penalties for violations. Security, by contrast, is largely shaped by industry frameworks and technical standards that organizations adopt voluntarily or under contractual pressure. Knowing which rules apply to each function helps you assign clear ownership and avoid the gaps that appear when both teams assume the other is handling a shared obligation.
The moment you understand which laws govern privacy and which frameworks govern security, accountability in your organization becomes much easier to establish.
Privacy laws that govern data collection and use
Privacy law exists to protect individuals, not organizations, and that distinction drives everything about how compliance works. Laws like the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the United States impose specific obligations on any organization that collects personal data about individuals in those jurisdictions, regardless of where your company is headquartered. Other sector-specific laws apply in targeted contexts:
- HIPAA governs the privacy of protected health information in healthcare settings
- FERPA protects student education records at institutions that receive federal funding
- COPPA restricts the collection of personal data from children under 13
- FDA 21 CFR Part 11 sets requirements for electronic records in regulated pharmaceutical and clinical environments
Your legal and compliance team owns this regulatory exposure, and they are responsible for mapping your data practices against the requirements of every applicable law.
Security standards that guide technical protection
Security is governed less by direct legislation and more by technical frameworks that define what good protection looks like. The NIST Cybersecurity Framework, published by the National Institute of Standards and Technology, gives organizations a structured way to identify, protect, detect, respond to, and recover from security threats. ISO/IEC 27001 is an internationally recognized standard for information security management systems and is often required by enterprise clients as a condition of doing business.
Some regulations do impose security requirements directly. GDPR Article 32 requires organizations to implement appropriate technical measures to protect personal data, which means your security team’s work directly supports your privacy compliance posture. Payment card security falls under PCI DSS, which mandates specific controls for any organization that processes card transactions. Your IT and cybersecurity team owns these frameworks, but your compliance team needs regular reporting from them to demonstrate that technical controls are in place and functioning.
How to improve privacy and security together
Improving data privacy and data security together is more efficient than running them as separate programs, because the foundational work for each discipline overlaps significantly. Rather than treating these as two independent projects competing for the same budget and attention, you can build a unified program that satisfies both sets of requirements without duplicating effort.
The organizations that handle data privacy vs data security most effectively are the ones that coordinate both disciplines under a shared governance structure from the start.
Start with a data inventory
You cannot protect data you have not mapped. A data inventory documents every category of personal information your organization collects, where it is stored, who can access it, and how long you retain it. This single artifact directly serves your privacy compliance requirements by showing regulators that you understand what data you hold, and it directly serves your security team by identifying which systems and databases need the strongest technical protections.
When building your inventory, capture at minimum:
- Data category (for example, employee training records or customer contact details)
- Storage location and system owner
- Access permissions and roles
- Retention period and deletion schedule
- Applicable privacy laws or contractual requirements
Align your teams on shared goals
Your legal and compliance team sets the rules for how data should be handled, and your IT and security team builds the technical controls that enforce those rules. These two groups often work separately by default, which creates gaps where neither team realizes a shared obligation exists. Schedule regular cross-functional reviews where both teams examine the same data inventory together, agree on which records carry the highest risk, and confirm that your technical controls actually match your written policies.
Shared accountability also extends to incident response planning. When you build your breach response plan, both teams need clearly defined roles before an incident happens. Your IT team handles technical containment while your legal team manages regulatory notification and stakeholder communication, and writing those responsibilities down in advance is what keeps the response organized when pressure is high.
Build controls that serve both disciplines
Several technical controls directly advance both your privacy posture and your security posture at the same time, which makes them the highest-value investments in your program. Role-based access control restricts who can view personal records, satisfying privacy requirements while functioning as a core security measure. Encryption protects data from unauthorized access, and audit logs give you the visibility to detect both policy violations and unauthorized system access through the same monitoring process.
Final takeaways
Data privacy and data security are not the same problem, and treating them as one leaves your organization exposed in ways you may not catch until something goes wrong. Privacy governs the rules around collecting and using personal data, while security provides the technical controls that keep that data out of the wrong hands. Both disciplines matter, and both require dedicated ownership, clear policies, and regular review.
When you approach data privacy vs data security as two complementary disciplines rather than one interchangeable concept, you build a stronger foundation for compliance, trust, and operational resilience. Your legal team sets the boundaries, your IT team enforces them, and your shared data governance work connects the two. Start with your data inventory, align your teams around shared goals, and invest in controls that serve both functions at once. If you are evaluating how a platform like Axis LMS can support compliant training delivery, take our LMS readiness quiz to find out where you stand.
