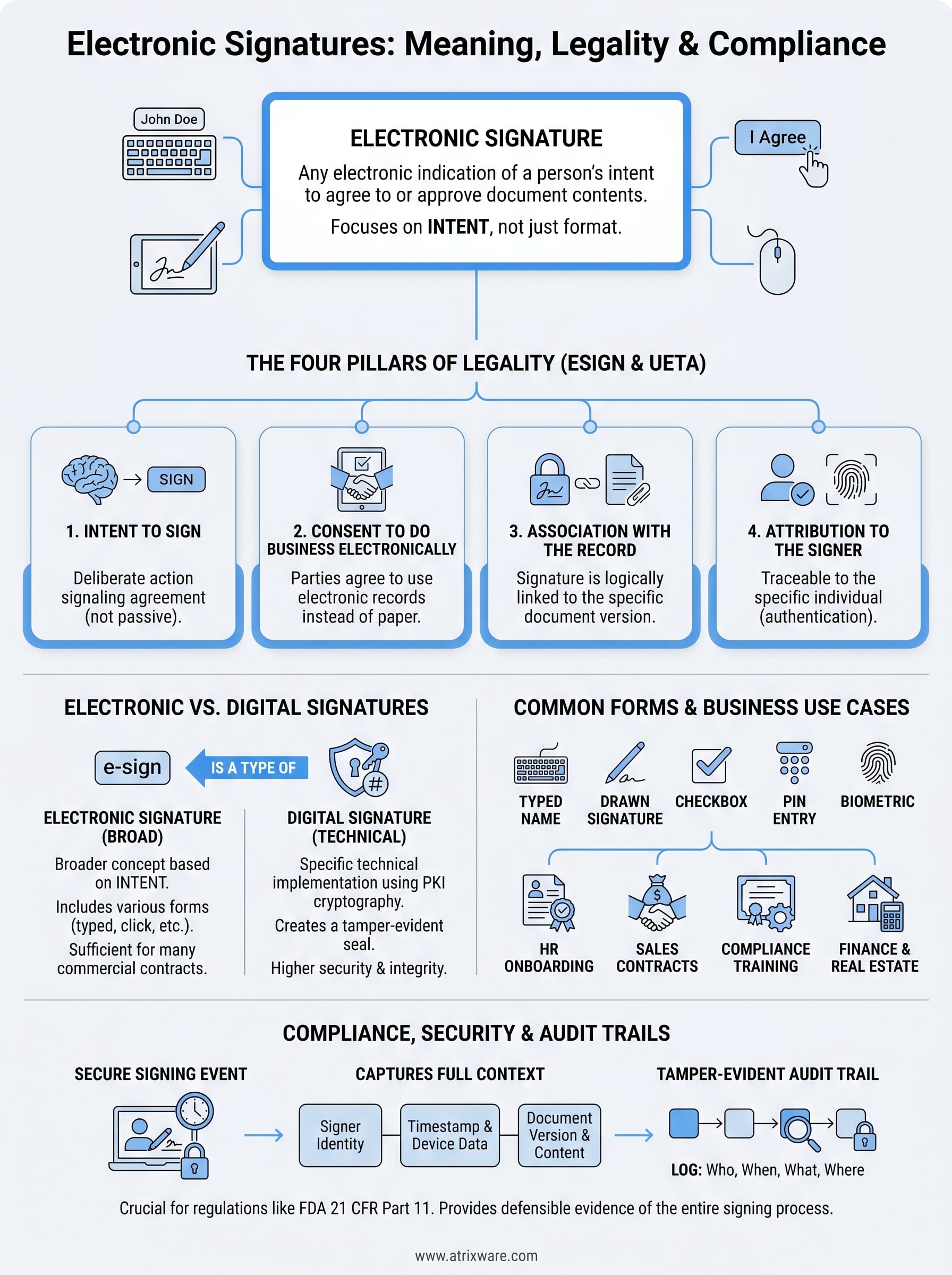
An electronic signature can be as simple as typing your name into a form field or as complex as a cryptographically secured approval on a regulated document. Despite how widespread they’ve become, the electronic signature definition still causes confusion, particularly when legal validity and compliance requirements enter the picture.
At its core, an electronic signature is any electronic indication of a person’s intent to agree to or approve the contents of a document. That sounds straightforward, but the details matter. Different laws, industries, and use cases impose different requirements on what qualifies as a valid e-signature, and getting it wrong can create real legal and regulatory exposure. For organizations managing compliance training through platforms like Axis LMS, where training acknowledgments, certification records, and audit trails must satisfy standards like FDA 21 CFR Part 11, understanding these distinctions isn’t optional, it’s foundational.
This article breaks down exactly what an electronic signature is, how it differs from a digital signature, what makes one legally binding, and where common examples appear across business operations. Whether you’re building compliant training workflows or evaluating how e-signatures fit into your organization’s processes, you’ll walk away with a clear, practical understanding of the term and its implications.
What counts as an electronic signature
The electronic signature definition under U.S. law is deliberately broad. The Electronic Signatures in Global and National Commerce (ESIGN) Act, passed in 2000, defines an electronic signature as "an electronic sound, symbol, or process, attached to or logically associated with a contract or other record and executed or adopted by a person with the intent to sign." That phrase "intent to sign" carries most of the legal weight. Without demonstrable intent, even a sophisticated digital mark doesn’t qualify as a valid signature.
The legal starting point
Both the ESIGN Act and the Uniform Electronic Transactions Act (UETA), which most states have adopted, share the same core requirement: the signature must reflect the signer’s conscious intent to agree. This requirement isn’t about the technology you use. It’s about whether the person understood what they were agreeing to and actively chose to sign. A signer who clicks through a form without understanding the action may not have provided a valid e-signature, regardless of what the system captured.
Intent is the legal threshold that separates a valid electronic signature from a meaningless click.
Forms an electronic signature can take
Because the legal definition focuses on intent rather than format, electronic signatures can take many different forms. This flexibility is one of the main reasons they’ve been widely adopted across industries. Here are the most common types you’ll encounter:

- Typed name: The signer types their name into a designated field at the end of a document or agreement.
- Drawn signature: The signer uses a mouse, stylus, or touchscreen to draw a replica of their handwritten signature.
- Scanned signature: A person signs a physical document, scans it, and attaches the image to a digital record.
- Checkbox or "I Agree" button: A click on a terms-of-service or acknowledgment form in a web interface.
- Email confirmation: In some contexts, a reply email confirming agreement to specific terms functions as an e-signature.
- PIN or password entry: Entering a unique credential to confirm identity and authorize a transaction.
- Biometric data: A fingerprint scan, voice confirmation, or facial recognition used to authenticate and approve.
Each of these carries a different level of evidentiary weight in a dispute. A typed name on a consumer contract sits at a different assurance level than a biometrically authenticated approval on a regulated pharmaceutical document. Knowing which type fits your specific situation prevents compliance gaps before they become legal problems.
What doesn’t qualify
Not every mark on a digital document counts as an electronic signature. An automatic timestamp, for example, records when a document was created or modified, but it doesn’t capture intent. Similarly, metadata embedded in a file confirms technical details about a document but says nothing about whether a specific person consciously agreed to its contents.
Forwarding a contract to someone via email also does not constitute their signature, even if they open and read it. The receiving party must take a deliberate, identifiable action that demonstrates their agreement. This distinction matters particularly in regulated environments, where auditors and courts look for clear evidence that a specific individual completed a specific affirmative act at a specific point in time. If your training completion records or policy acknowledgments rely on passive events rather than active confirmation, they may not hold up under scrutiny.
How electronic signatures work in practice
Understanding the electronic signature definition is one thing; seeing how the process actually runs is another. When you apply an e-signature to a document, several things happen in sequence, and each step contributes to whether the signature is legally defensible and auditable later.
The signature capture process
When you open a document for signing, the system presents the content you’re agreeing to and then prompts you to take a deliberate action: typing your name, drawing a signature, clicking a confirmation button, or entering a credential. That action gets recorded along with a timestamp and session data that ties your specific identity to the specific version of the document at that exact moment.
The capture event is the moment that transforms intent into a legally recognizable act.
The system doesn’t just store the mark itself. It packages the surrounding context, including what document you saw, when you saw it, and what action confirmed your agreement. This packaging is what allows a platform to reconstruct the full signing event if a dispute arises later.
Authentication and what gets recorded
Authentication is how the system confirms you are who you say you are before accepting your signature. At its simplest, this means you’ve logged in with credentials tied to your identity. More rigorous implementations add a second factor, such as a one-time code sent to your phone or email, before the system accepts the signature. Regulated industries often require multi-factor authentication because a signature that can’t be traced back to a verified individual carries far less legal and compliance weight.
After you sign, the platform generates an audit trail that documents who signed, when they signed, what version of the document they signed, and additional details like the signer’s IP address and the device used. Many platforms store this record as a tamper-evident log, meaning any attempt to alter the document or its associated data becomes detectable. For compliance-heavy environments, that audit trail isn’t just a useful feature; it’s often a hard regulatory requirement that determines whether your signed records will hold up under review.
Are electronic signatures legal in the US
Yes, electronic signatures are fully legal across the United States for the vast majority of contracts and business documents. Federal law established this baseline in 2000, and the framework has held steady since. Understanding why requires looking at how the legal architecture actually works, because the rules aren’t uniform across every situation, and some important exceptions still apply.
The ESIGN Act and UETA
The ESIGN Act, passed by Congress in 2000, gave electronic signatures the same legal standing as handwritten signatures for transactions affecting interstate commerce. That covers most commercial agreements businesses deal with daily. Around the same time, the Uniform Electronic Transactions Act (UETA) was developed and has since been adopted by 49 states plus the District of Columbia and the U.S. Virgin Islands. UETA addresses transactions at the state level and fills in the gaps the federal ESIGN Act doesn’t reach. Together, these two laws create a consistent legal foundation that allows businesses to replace paper-based signing with electronic alternatives without losing enforceability.
The combination of the ESIGN Act and UETA means that for most commercial purposes, an electronic signature carries the same legal weight as ink on paper.
Under both laws, no specific technology or format is required. What matters is that the signature reflects genuine intent and that the parties agreed to conduct the transaction electronically. This is precisely why the electronic signature definition under U.S. law focuses on intent rather than the method used to capture the signature.
Exceptions where e-signatures don’t apply
Not every document can be signed electronically under U.S. law. Both the ESIGN Act and UETA carve out specific categories that still require handwritten signatures or traditional paper records. If your work touches any of these areas, you need to verify whether an e-signature will hold before relying on it.
Documents that typically fall outside e-signature coverage include:
- Wills, codicils, and testamentary trusts: These require physical signatures and witnesses in most states.
- Court orders and official court documents: Judicial processes follow their own procedural rules.
- Notices of cancellation for utilities or insurance: Certain consumer protection documents require paper.
- Documents governed by the Uniform Commercial Code (UCC): Specifically, negotiable instruments like checks.
- Family law documents: Including adoption papers and certain divorce filings.
Knowing these exceptions protects your organization from relying on an invalid signature in a situation where it could expose you to legal or regulatory risk.
The four requirements for a valid e-signature
Legality doesn’t come automatically just because someone clicks a button or types a name. Both the ESIGN Act and UETA point to four distinct requirements that every valid electronic signature must satisfy. If any one of these is missing, the signature may not hold up in a dispute, a regulatory audit, or a court proceeding. Understanding the electronic signature definition at a practical level means understanding these four conditions, not just the broad legal language.
Intent to sign
Intent is the foundational requirement. The signer must take a deliberate action that signals agreement, not a passive or accidental one. This is why well-designed signing workflows present the full document text, clearly label the signature field, and require an affirmative confirmation step before recording the signature. If a signer can credibly argue they didn’t understand they were signing anything, the intent requirement fails.
A system that buries the signature action inside a cluttered workflow creates legal risk even when everything else is technically correct.
Consent to do business electronically
Both parties must agree to conduct the transaction electronically rather than on paper. For businesses, this typically means including a consumer disclosure at the start of a signing flow that explains the electronic process and gives the signer the option to receive a paper copy instead. Skipping this step is one of the most common ways organizations unknowingly undermine otherwise valid e-signatures.
Association with the record
The signature must be logically associated with the specific document being signed. Storing a signature image in a separate file that isn’t tied to the exact version of the document the signer reviewed breaks this requirement. Your platform must link the signature data directly to the document content at the moment of signing, so there’s no question about which version the person agreed to.
Attribution to the signer
Attribution means the signature can be traced back to the specific individual who applied it. This is where authentication matters directly. A signature captured after a verified login, and ideally after a second authentication factor, carries far stronger attribution than one collected with no identity verification at all. The more robust your authentication process, the harder it is for someone to dispute that they were the one who signed. For compliance-heavy workflows, strong attribution often determines whether your records survive regulatory scrutiny.
Electronic vs digital signatures
The terms electronic signature and digital signature get used interchangeably all the time, but they describe two different things. The electronic signature definition is the broader concept: any electronic indication of intent to sign. A digital signature is a specific technical implementation that falls within that broader category. Every digital signature is an electronic signature, but not every electronic signature is a digital signature.
What a digital signature actually is
A digital signature uses public key infrastructure (PKI) cryptography to secure the signing process. When you apply a digital signature, the system generates a unique mathematical value, called a hash, based on the document’s content. It then encrypts that hash with your private key. Anyone with your public key can decrypt it and verify that the document hasn’t been altered since you signed it. If even a single character changes after signing, the hash no longer matches and the tampering becomes immediately detectable.
Digital signatures don’t just confirm who signed; they confirm that what you signed is exactly what the other party now holds.
This cryptographic binding is what separates digital signatures from simpler forms like a typed name or a drawn signature. Both carry legal validity under the ESIGN Act, but a digital signature provides a much stronger technical guarantee of document integrity and signer identity.
Why the distinction matters for compliance
For most standard business agreements, a basic electronic signature is sufficient. Employment offer letters, vendor contracts, and software license agreements typically don’t require the additional technical guarantees that PKI provides. Your signing workflow can rely on a typed name or a click-through confirmation, and it holds up legally.
Regulated industries operate under different rules. FDA 21 CFR Part 11, which governs electronic records in pharmaceutical and life sciences environments, requires controls that align closely with what digital signatures provide, including secure, verifiable links between the signature and the signer’s identity and protections against document alteration. Similarly, certain financial services and government contracts specify digital signature standards rather than accepting any electronic mark.
Choosing between the two comes down to your specific regulatory context and risk tolerance. If your organization operates outside heavily regulated industries, a standard electronic signature process handles the vast majority of your needs. If you manage documents subject to FDA oversight, government security requirements, or contractual mandates for PKI-based signing, you need a solution that delivers cryptographic verification, not just a captured mark.
Common examples and where businesses use them
The broad electronic signature definition under U.S. law translates directly into widespread adoption across virtually every business function that requires documented agreement. Knowing where other organizations apply e-signatures helps you identify the workflows in your own operations that could benefit from replacing paper-based signing.
HR and employee onboarding
HR teams were among the earliest adopters of electronic signatures because the volume of paperwork involved in hiring and onboarding makes manual signing a bottleneck. Offer letters, benefits enrollment forms, direct deposit authorizations, and confidentiality agreements all require the employee’s acknowledged consent before work begins. With e-signatures, your HR team can send these documents digitally, capture signed returns within hours, and store everything in a centralized, searchable record without managing physical files.
Customer-facing agreements and sales contracts
Sales organizations use electronic signatures to accelerate contract cycles and reduce the time between verbal agreement and signed deal. Service agreements, subscription contracts, statements of work, and order forms are all standard candidates. When a prospect can review and sign a proposal from their phone without printing anything, your deal closes faster and with less friction on both sides.
The reduction in signing delays often matters more to the business outcome than the legal formality of the signature itself.
Compliance training and policy acknowledgments
Organizations subject to regulatory requirements use e-signatures to confirm that employees have reviewed and understood required training content, updated policies, and compliance procedures. This is particularly common in industries governed by FDA regulations, financial services oversight, and workplace safety standards. Each signed acknowledgment becomes a timestamped record that demonstrates your workforce completed the required training and accepted the associated obligations. For platforms like Axis LMS, this means every course completion or policy review can carry a captured signature that feeds directly into your audit trail.
Financial services and real estate transactions
Banks, mortgage lenders, and real estate firms rely on electronic signatures for loan documents, property disclosures, closing packages, and account opening forms. Regulatory guidance from agencies like the Consumer Financial Protection Bureau supports their use in most consumer lending contexts, which has accelerated adoption across the sector. Real estate transactions in particular benefit from e-signatures because multiple parties in different locations need to execute the same set of documents on a tight timeline.
Security, audit trails, and compliance basics
Security and compliance aren’t separate concerns from the electronic signature definition; they determine whether your signed records hold up when they’re actually tested. Every time someone applies a signature, the platform should capture far more than just the mark itself. The full signing event, including the signer’s verified identity, the document version, the timestamp, and the session context, forms the foundation of a defensible record that survives both legal disputes and regulatory audits.
What a secure signing platform records
A well-built signing platform generates a tamper-evident audit trail that follows every document throughout its lifecycle. This log captures who signed, when they signed, what device and IP address were involved, and which authentication method confirmed the signer’s identity. If someone later disputes whether they signed or claims the document was altered, your audit trail provides the evidence that resolves the question directly rather than leaving room for credible denial.
A complete audit trail transforms a signature from a simple mark into a verifiable chain of custody.
Beyond the log itself, many platforms apply cryptographic hashing to the document at the moment of signing. The hash locks the document’s exact state so any subsequent change, even a minor formatting edit, produces a detectable mismatch. This technical control is what gives your signed records durability against challenge and adds a layer of protection that simple captured marks alone cannot provide.
Meeting compliance requirements
Regulatory frameworks in specific industries impose stricter controls than the baseline requirements under the ESIGN Act. FDA 21 CFR Part 11, for example, requires that electronic signatures in pharmaceutical and life sciences environments include the signer’s printed name, the date and time of signing, and the meaning of the signature, such as whether it represents authorship, review, or approval. Your signing workflow must capture and display all three elements for each signature to satisfy the regulation.
Financial services organizations face similar requirements under their own oversight frameworks, and government contractors often follow the NIST Digital Identity Guidelines, which specify authentication assurance levels for different transaction types. Understanding which framework governs your specific documents tells you precisely how much security your signing process requires. You don’t need to over-engineer a standard vendor agreement, but you do need to match your technical controls to your regulatory obligations. Mapping your document types to their applicable requirements before you configure your signing workflows prevents compliance gaps that typically surface at the worst possible time, during an active audit or legal dispute.
Wrap-up and next steps
The electronic signature definition comes down to one core principle: a deliberate, attributable electronic act that signals clear intent to agree. From typed names to cryptographically secured digital signatures, the format matters less than whether your process captures intent, authenticates the signer, ties the signature to the exact document, and generates a defensible audit trail. Each of those four elements directly determines whether your signed records hold up in a legal dispute or a regulatory review.
For organizations that deliver compliance training, policy acknowledgments, or certification workflows, the stakes are especially high. Your training records need to function as evidence, not just data. If you’re evaluating whether your current training platform meets those standards, take the Axis LMS readiness quiz to see where you stand and what your next step should be.